When Surveillance is a Strategy: How Hacked Cameras and Mobile Networks Are Redefining Today's Wars?
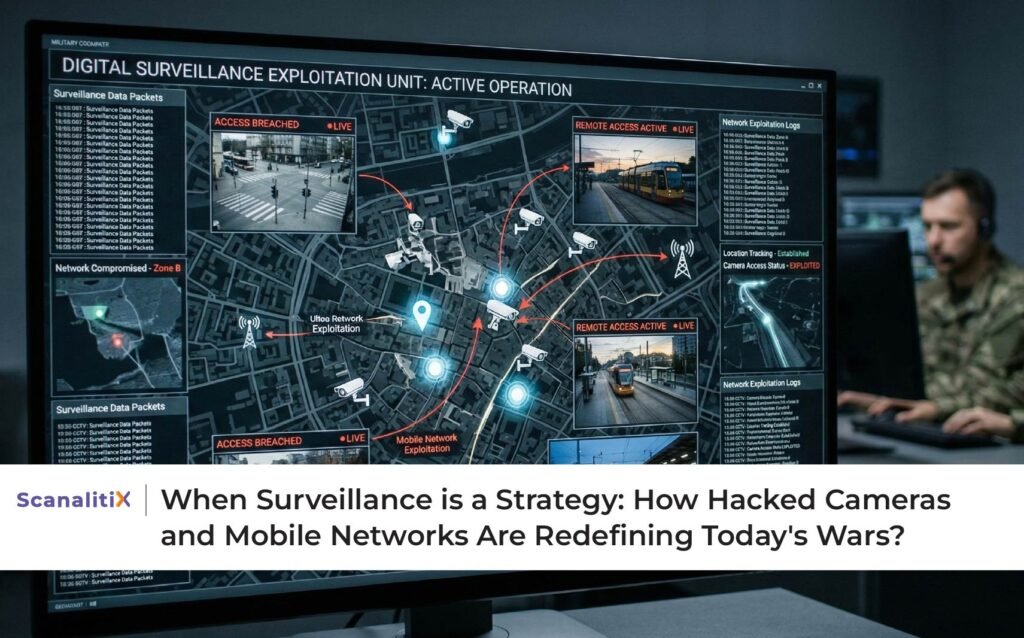
Table of Contents
Recent global headlines have highlighted a chilling reality of modern conflict. According to reports, intelligence operations allegedly leveraged hacked traffic cameras and compromised mobile phone networks to track and eliminate a high-value target during escalating tensions between Israel and Iran. While details continue to unfold, one fact stands clear: surveillance systems are no longer just tools of public safety or urban management. They have become strategic assets in geopolitical conflict.
The news report describing how digital surveillance infrastructure was allegedly exploited highlights a broader shift in the global security landscape. In the age of AI, connected devices, and pervasive digital networks, data is power. Cameras and mobile signals, once viewed as neutral utilities, can become intelligence channels in high-stakes scenarios.
This development forces an urgent conversation about cybersecurity in surveillance systems, the weaponization of digital infrastructure, and the importance of secure AI-powered monitoring platforms.
The Weaponization of Everyday Infrastructure
Traffic cameras, cellular towers, public surveillance grids, and IoT-enabled systems are integral to modern urban life. They manage traffic flow, enhance public safety, and support emergency response. However, when improperly secured, these same systems can be exploited.
Cybersecurity experts have long warned about vulnerabilities in connected surveillance infrastructure. A report by the Cybersecurity and Infrastructure Security Agency (CISA) has emphasized that networked cameras and IoT systems can become entry points for sophisticated cyber intrusions if not adequately protected.
The alleged use of hacked traffic cameras and telecom networks in a military context reflects a disturbing but logical evolution. When surveillance systems are connected to central databases, and when mobile networks generate continuous location metadata, they create detailed movement patterns. If accessed unlawfully, such data can reveal routes, habits, and strategic positioning.
According to a 2023 report by IBM on cybersecurity trends, nation-state cyber operations increasingly target civilian infrastructure as part of broader intelligence and warfare strategies. Surveillance and telecommunications systems are particularly attractive because they provide real-time geospatial intelligence.
In this context, surveillance is no longer passive. It is strategic.
Mobile Networks as Tracking Tools
Mobile phones constantly communicate with cell towers, generating metadata about location and movement. While this data is typically anonymized and protected under privacy regulations, breaches or sophisticated cyber operations can expose patterns.
Research published by the Electronic Frontier Foundation (EFF) has documented how mobile metadata can reveal sensitive information, even without direct content access. Location tracking, signal triangulation, and network logs can collectively create highly precise movement maps.
In high-conflict environments, such intelligence becomes invaluable. Tracking a device’s location in real time can provide actionable data for military or security operations.
This reality highlights a broader concern. As digital infrastructure becomes deeply embedded in daily life, securing telecom and surveillance systems becomes a matter of national security.
The Role of AI in Surveillance and Targeting
Artificial Intelligence amplifies the capabilities of surveillance systems. AI-powered video analytics can process vast amounts of footage in real time, identifying specific vehicles, faces, or movement patterns. When combined with mobile network data, the intelligence potential increases exponentially.
According to MarketsandMarkets, the global AI video analytics market is expanding rapidly, driven by demand across defense, smart cities, and public safety sectors. AI enables pattern recognition at a scale and speed that human analysts cannot match.
However, the same capabilities that enhance public safety can be misused if governance and security fail.
The World Economic Forum has warned that as AI becomes integrated into surveillance systems, robust cybersecurity frameworks and ethical oversight must accompany deployment. Without strong safeguards, AI-driven infrastructure can be manipulated for harmful purposes.
Cybersecurity: The Weakest Link in Surveillance Networks
The recent events bring attention to a crucial issue: many public surveillance systems were not originally designed with military-grade cybersecurity in mind. Cameras deployed for traffic management or municipal monitoring often operate on networks that may lack advanced encryption, segmentation, or intrusion detection.
The Verizon Data Breach Investigations Report consistently identifies misconfigured devices and unsecured endpoints as major contributors to cyber incidents. IoT devices, including cameras, remain frequent targets.
When surveillance networks connect to centralized monitoring centers without adequate safeguards, they create potential vulnerabilities. A compromised camera feed does not merely expose video. It may provide access to broader systems, including location databases and communication networks.
Securing surveillance infrastructure is no longer optional. It is imperative.
Balancing Surveillance Power with Responsible Governance
The strategic use of surveillance systems in conflict zones raises ethical and governance questions. Surveillance infrastructure exists primarily to enhance civilian safety and operational efficiency. When such systems are exploited, public trust erodes.
Governments and enterprises must ensure that surveillance deployments incorporate strong encryption, network segmentation, multi-factor authentication, and continuous threat monitoring. The European Union Agency for Cybersecurity (ENISA) emphasizes that critical infrastructure operators must adopt zero-trust architectures and continuous risk assessment models.
Transparency also plays a role. Citizens are more likely to accept surveillance when they understand its purpose, governance framework, and security safeguards.
AI-powered surveillance should empower safety, not become a vulnerability.
SEO Insight: Why Secure AI Surveillance Matters Today
Search trends increasingly reflect concerns around cybersecurity in surveillance systems, AI video analytics security, and infrastructure protection. As smart cities expand and AI-powered monitoring becomes widespread, the intersection of surveillance and cyber defense grows more critical.
Key SEO themes emerging from global discourse include:
- AI surveillance cybersecurity
- Secure video analytics platforms
- Smart city surveillance risks
- IoT camera vulnerabilities
- Cybersecurity in public infrastructure
These topics reflect both public interest and enterprise urgency.
Lessons for Enterprises and Governments
The alleged exploitation of surveillance and telecom systems in conflict underscores a universal lesson. Any connected infrastructure, if unsecured, can become a liability.
Enterprises deploying surveillance across campuses, warehouses, retail chains, or financial institutions must prioritize cybersecurity alongside analytics capability. Similarly, governments building smart city networks must integrate AI intelligence with hardened digital defenses.
The goal is twofold: harness the power of AI surveillance while protecting it from misuse.
Where Scanalitix Fits In
In a world where surveillance can shape strategic outcomes, platforms must combine intelligence with resilience.
Scanalitix approaches AI-powered surveillance as a secure, unified ecosystem. By integrating video management systems, AI analytics, centralized monitoring, and structured workflows within a robust architecture, it reduces fragmentation and strengthens oversight.
The platform emphasizes secure deployment models, controlled access, and scalable integration across edge and cloud environments. Rather than exposing disparate camera networks, it centralizes governance while maintaining encryption and compliance standards.
Scanalitix enables organizations to extract actionable intelligence from video without compromising cybersecurity. It recognizes that modern surveillance must be both intelligent and secure.
In today’s digital landscape, intelligence without security is a risk. Security without intelligence is incomplete. Scanalitix quietly bridges both.
Conclusion
The evolving nature of global conflict has revealed an uncomfortable truth: digital infrastructure can become a strategic battlefield. Traffic cameras, mobile networks, and AI-powered surveillance systems are no longer neutral utilities. They are powerful intelligence assets.
The recent reports highlight the urgent need to secure surveillance networks against exploitation. As AI continues to enhance monitoring capabilities, cybersecurity must evolve in parallel.
For cities, enterprises, and governments, the lesson is clear. Invest not only in smarter surveillance but in safer surveillance.
Because in the age of AI, visibility is power. And power must be protected.
